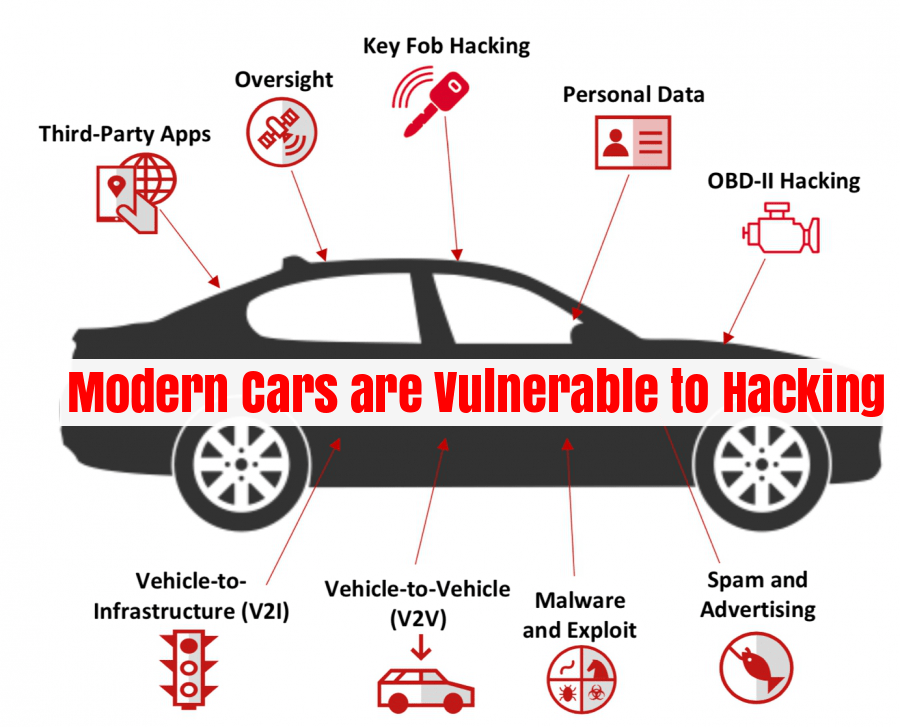
As vehicles are increasingly computerized, researchers and industry officials consider it inevitable that cars will face the same vulnerabilities as PCs. Internal computer networks monitor and control everything from brakes, engines and transmissions to air bags and keyless-entry functions. Wireless connections, meanwhile, are becoming more common in reporting a vehicle’s position or providing information about the car’s functions. Some auto companies are creating applications to allow users to control some features in their car with their smartphone.
On 10 March, 2011 there was a news update that “Researchers had found that Cars can be hacked and remotely controlled“. You can refer the link here to read the news: Could the computer in your car be hacked?
Key findings of the research work carried out by Stefan Savage, a University of California, San Diego, computer science professor and Yoshi Kohno, a computer science professor at the University of Washington are:
- able to “bypass rudimentary network security protections within the car”
- “adversarially cont” adversarially control a wide range of automotive functions and completely ignore driver input — including disabling the brakes, selectively braking individual wheels on demand, stopping the engine and so on”
- an attack could embed malicious code in a vehicle and then erase any evidence of its presence after a crash
- found ways to compromise security remotely, through wireless interfaces like Bluetooth, mechanics’ tools and even audio files.
- In one example, a modified song in a digital audio format could compromise the car’s CD player and infect other systems in the vehicle.
- Researchers were able to “obtain complete control” over the car by placing a call to the vehicle’s cell phone number and playing an audio signal that compromised the vehicle.
Key findings of Research teams at Rutgers University and the University of South Carolina:
- showed vulnerabilities of in-car wireless networks that operate tire-pressure monitoring systems that tell motorists if their tire needs more air. From a distance of 40 meters, they bypassed security to tap into information identifying the tire and tire pressure of cars driving down the road.
Some important quotes to be noted are:
- “I hope it’s more of a warning for the engineering groups that certain systems are vulnerable,” said Ivan Seskar, associate director for information technology at the Wireless Information Network Laboratory at Rutgers University.
- “When people first started connecting their PCs to the Internet, there wasn’t any threat, and then over time it manifests,” said Stefan Savage, a University of California, San Diego, computer science professor who conducted the research. “The automotive industry, I think, has the benefit of the experience of what we went through.”
The United States Council for Automotive Research, a group funded by Detroit’s auto companies, is also forming a task force to study the issue, said spokeswoman Susan Bairley.
Research Papers can be accessed from here.
Looking for a Solution
Security in automobile is becoming priority number one for the manufacturers. The share of electronic components inside cars is larger than ever and the reliability of these software components has become of prime concern. Consortia (Autosar, Jaspar,…) between manufacturers are created in order to standardize the management software of the electronic systems for the automobile industry.Different security needs have been explored by the automobile industry including:
- the need to secure the security software components on board the cars (starting system, braking system, and ABS urgency braking system…)
- the securing of the control station updates for the manufacturer car dealers.
- the need for quality control by software certification especially for subcontracted software.
Validy Technology, by ensuring the integrity of the embedded software, protects all the equipments from all possible forms of piracy.
Last Updated on: March 14, 2011
