Someone referred me to the UNREMOTE link where an interesting article was posted about a tool named as “Browser Forensic Tool (BFT)”. The link is given below:
http://unremote.org/2012/02/09/bft-browser-forensic-tool/
About BFT:According to the above given link, BFT is a software that will search in all kind of browser history (even archived) in few seconds. It will retrieve URLs and Title with chosen keywords of all matching search. One can use default example profiles or create a new one, with thematic search.
At first hand since never heard something like this, hence, it was obvious for me to take BFT for a test ride and to know whether it is worth using or not.
Additionally, the website BrotherSoft‘s Publisher also gives the following comment on BFT as:
You wan’t to search very quickly in the History of all common browsers
Reference: http://www.brothersoft.com/browser-forensic-tool-486857.html
even archived ones by keywords list (manageable) ?
This software is made for you, for companies, anti cyber criminal companies,
for particular this software will simplify your life and save hours of manual researching. you can free download Browser Forensic Tool 1.0 now.
Hence, I installed it in a Virtual Machine having an Operating System of Microsoft Windows 7 Professional Version with all the necessary Security Tools installed viz. Anti-Virus, Intrusion Detection System (IDS), Wireshark etc.
On the first hand, the given link for downloading installs a file given below:
File Name: BrowserForensicTool_downloader_by_BrowserForensicTool.exe
CRC32: 461b63c5
MD5: 0e409b01ef99c9e6d65bdbb94d9e5592
SHA-1: b85f13c7255a6d52597860fd51a14b499729d583
File Size: 154.5 KB
The icon used by the above installer is:
When the file’s properties were checked following information was observed:
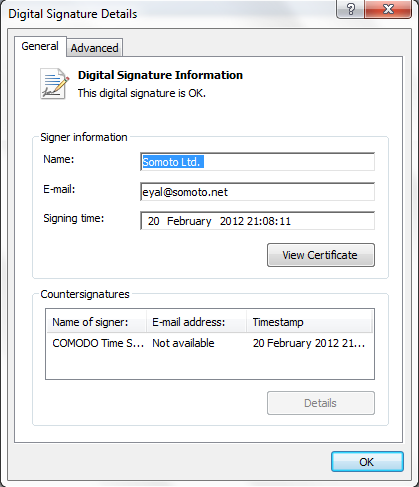
It was interesting to find that this tool is having a digital signature signed by COMODO too:
After executing the file with a double click, it installs another executable named as “BetterInstaller.exe”. This file silently gets extracted in the following directory path:
C:\Users\\AppData\Local\TempDir
The Icon Image of the application is:
Further information about Better Installer is given below:
File Name: BetterInstaller.exe
CRC: 65f69cd7
MD5: d79b88bab3231ebebd3c6505ab68ce56
SHA-1: 3222e8dab740ba1d640cc66a9cd36070969deb80
Size: 207 KB
File Properties:
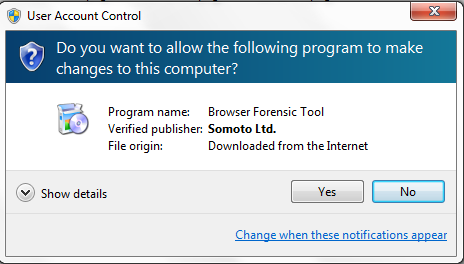
Once the user clicks on the above installer, it will show that it is preparing the Browser Forensic Tool (BFT) to initiate the process.
Since Endpoint Protection was installed in the Virtual Machine, following message was displayed:
As it can be seen from the above image, it was trying to connect to installer.filebulldog.com having remote IP address 78.138.98.55 which is based in Germany and is assigned to MESH GmbH. The IP Address route map is given below:
I had tried to connect to this IP via the above application numerous times but no installation continued. Instead it always showed that this file is in the mode of preparing BFT for installation to continue further installation.
From this point onwards, it was a matter of concern for me that why even having an internet connection of 4Mbps and other files still getting downloaded from other websites this file isn’t able to download anything!
Something is suspicious and probably malicious in nature!! Probably it is connecting to the remote location and extracting the user’s data and transferring it to the above mentioned IP Address. Possessing a Digital Signature was giving a signal that it is a benign file but the way it was working was looking like it is otherwise. Hence, it was decided to carry out the cyber investigation further.
Further information about this file BetterInstaller.exe was obtained after using the malware analysis tool – IDA Pro:
1 VERSIONINFO
FILEVERSION 1,0,0,0
PRODUCTVERSION 1,0,0,0
FILEOS 0x4
FILETYPE 0x1
{
BLOCK “StringFileInfo”
{
BLOCK “000004e4”
{
VALUE “CompanyName”, “Somoto Ltd.”
VALUE “CompanyWebsite”, “www.FileBulldog.com”
VALUE “FileDescription”, “”
VALUE “FileVersion”, “1.0”
VALUE “LegalCopyright”, “”
VALUE “ProductName”, “Better Installer”
VALUE “ProductVersion”, “1.0”
}
}
BLOCK “VarFileInfo”
{
VALUE “Translation”, 0x0000 0x04E4
}
}
Information in XML format is:

Registry Details obtained was:
HKCR
{
NoRemove AppID
{
‘%APPID%’ = s ‘BetterInstaller’
‘BetterInstaller.EXE’
{
val AppID = s ‘%APPID%’
}
}
}
Furthermore it was found that on WOT (Web Of Trust), some users had posted it as Malicious Content, and blocked by ESET. Screenshot is attached for the same:
The comments and further information can be read from here:
http://www.mywot.com/en/scorecard/betterinstaller.com
As the above comment shows a website link of scumware, as soon as I reached there it was more than sufficient to decide whether the Browser Forensic Tool is benign in nature or malign in nature. One can find this information right from the given link:
http://www.scumware.org/report/downloadcdn.betterinstaller.com
From the above website, following snapshot was taken:

The above image clearly shows that its’ a Trojan. In addition to this, after performing malware analysis on my virtual machine I had found that it is trying to inject an HTML Script in the browser which may read the installed cookies in the system.
By the way, MalwareBytes’ AntiMalware installed in the virtual machine showed following:
In nutshell, this tool does nothing as stated in the BrotherSoft website, hence, anything that sounds too good to be true must come under radar of suspicion and should not be allowed to go through after reading anything on the Software Download Provider’s websites. It can be deadly for your privacy, integrity of data, confidentiality of critical data as well as your computer system’s health.
Watch before taking another step in the cyberspace….
Last Updated: April 24, 2012